VINHOMES ĐAN PHƯỢNG WONDER PARK - TÂM ĐIỂM CUỘC SỐNG PHÍA TÂY HÀ NỘI
Vinhomes Đan Phượng sẽ là trung tâm đô thị mới của quận Đan Phượng và là điểm đến thu hút lượng cư dân và du khách hàng đầu ở khu vực phía Tây trung tâm Hà Nội. Được kỳ vọng trở thành biểu tượng kinh tế - du lịch của cả khu vực phía Tây thủ đô, Vinhomes Đan Phượng đang được kiến tạo tại địa bàn hai xã Tân Hội, Liên Trung. Sau một thời gian dài khảo sát kỹ lưỡng, tập đoàn Vingroup đã quyết định sẽ dựng lên ở nơi đây một đại đô thị “xanh” mang tầm vóc quốc tế, đem đến sự thịnh vượng cho cả khu vực Đan Phượng trong tương lai, nhất là khi nơi đây sẽ trở thành quận trong thời gian tới.
MỞ BÁN BIỆT THỰ LIỀN KỀ & NHÀ VƯỜN VINHOMES ĐAN PHƯỢNG GIAI ĐOẠN 1
- Biệt thự liền kề :
Diện tích : 72m2, 80m2, 96m2
Mặt tiền : 8 x 9m; 8 x 10m; 8 x 12m
Đường trước nhà : 10 - 13m
Xây thô hoàn thiện mặt ngoài 4 tầng, mật độ xây dựng 75%
Diện tích xây dựng :230 - 280 m2
- Biệt thự Nhà Vườn :
Diện tích : 110m2, 120m2
Mặt tiền : 8 x 13,75m; 8 x 15m
Đường trước nhà : 10 - 13 - 24m
Xây thô hoàn thiện mặt ngoài 4 tầng, mật độ xây dựng 75%
Diện tích xây dựng :320 m2 - 360 m2
NHÀ PHỐ SHOPHOUSE VINHOMES ĐAN PHƯỢNG GIAI ĐOẠN 1
- Nhà phố Shophouse
Diện tích: 96,120,130,150 m2 (mặt tiền từ 8m)
Đang cập nhật ....
THÔNG TIN CHUNG CƯ VINHOMES ĐAN PHƯỢNG CẬP NHẬT ...
- Phân khu hỗn hợp cao tầng Chung cư Vinhomes tại Đan Phượng dự kiến bao gồm :
+ Văn Phòng và Căn hộ & Phát triển theo khu shop Royal
Vị trí : Phân khu Chung cư Cao tầng dự kiến sẽ nằm sát đường----> để có nhiều diện tích làm tiện ích cảnh quan gần khu thấp tầng.
Cảnh quan 14 ha ( lấy cảm hứng từ Chicago )
Tiện ích Sport Zone :
- Bể bơi mái kính, tạo sóng, nhiệt đới,..
- Công viên Gym, BBQ, diện tích 7000 m2
- Công Viên Hạnh Phúc
- Tiện ích tiệc cưới, vườn khiêu vũ, vườn tình yêu ,...
- Family zone : Dịch Vụ cư dân, golf, hồ câu,...
- Zen Zone : Vườn Thiền,..
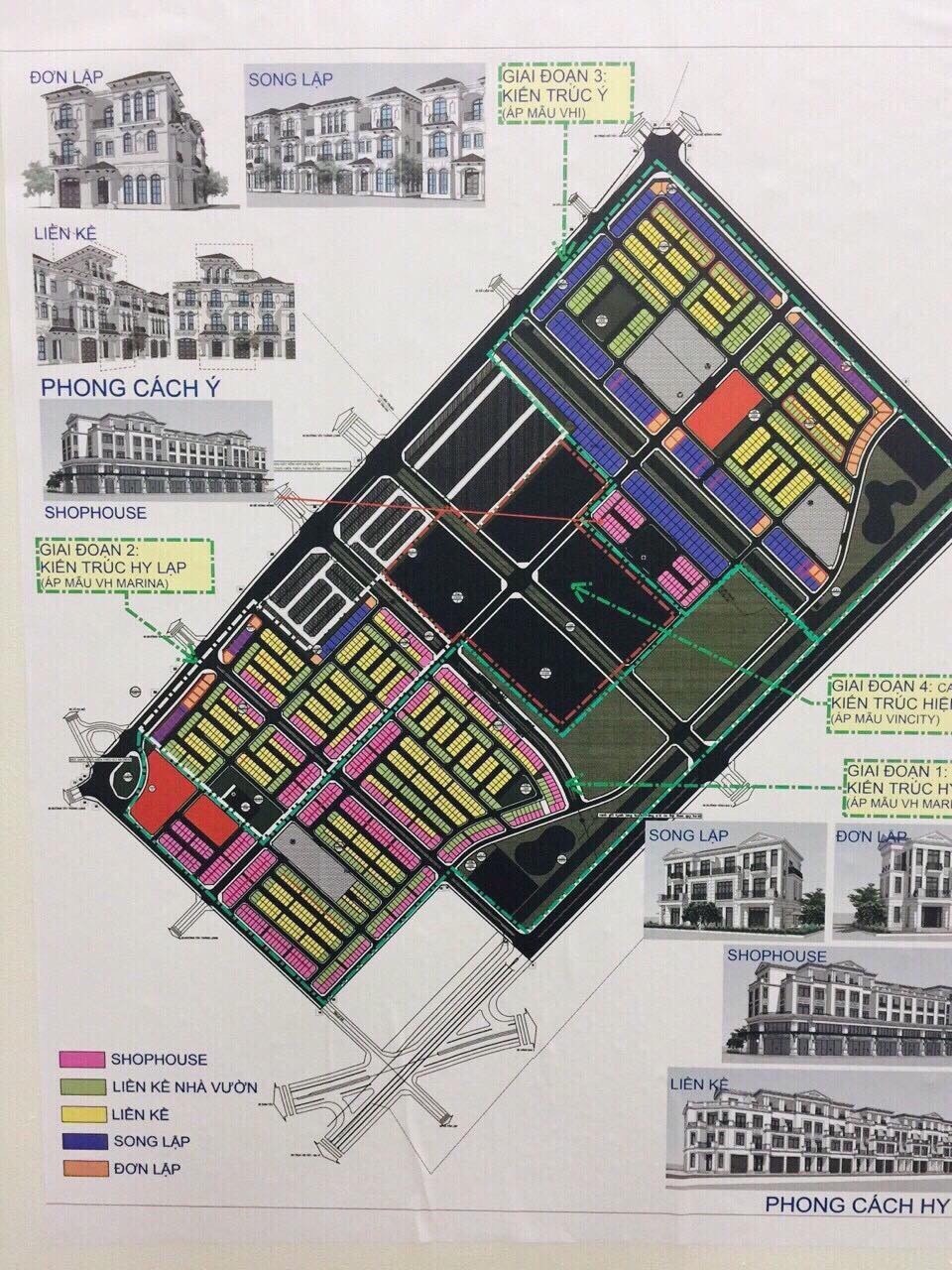
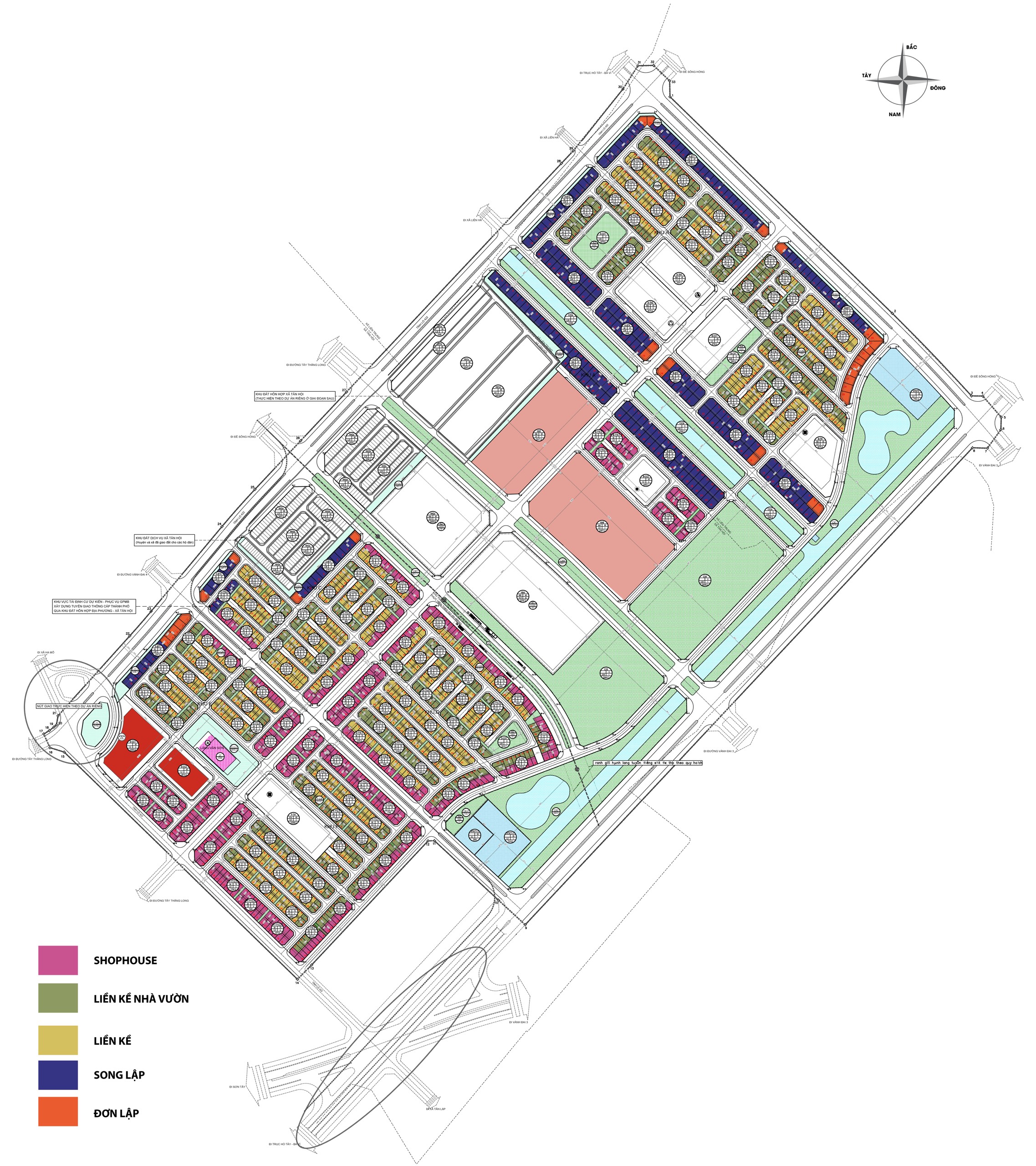
 Mặt bằng phân khu biệt thự vinhomes đan phượng dự kiến mở bán đợt 1
Mặt bằng phân khu biệt thự vinhomes đan phượng dự kiến mở bán đợt 1
KHU ĐÔ THỊ PHỨC HỢP VINHOMES ĐAN PHƯỢNG - HÀ NỘI
Tên dự án: Dự án Vinhomes Wonder Park Đan Phượng
- Phá lý bất động sản: Sở hữu sổ đỏ lâu dài
- Vị trí: Thuộc 2 xã Tân Hội & Liên Trung, huyện Đan Phượng, Tp. Hà Nội
- Chủ đầu tư dự án : Tập đoàn Vingroup
- Tổng diện tích quy hoạch dự kiến: 133ha.
Các phân khu chính trong dự án Vinhomes Đan Phượng
1. Phân Khu the Times nằm sát khu TTTM Vincom ( chạy theo concept thành phố sầm uất nhộn nhịp )
2. Phân Khu The Light : Phân khu Ánh Dương
- Có đại lộ ánh sáng
- Cây Ánh Sáng
- Gần cụm tiện ích cảnh quan
- Hệ Thống Trường học có : 3 trường liên cấp Vinschool, 1 trường ngoài
3. Phân Khu The Royal
- Biệt Thự Song lập
- Có Công Viên Nội Khu
- Trường Học
- Phòng Khám Vinmec
* Các loại hình căn hộ được hoạch : Căn hộ chung cư, BT Liền kề, BT Song lập, BT Đơn lập, Nhà phố Shophouse
- Phía Đông giáp huyện Mê Linh
- Phía Tây giáp huyện Phúc Thọ.
- Phía Bắc giáp quận Bắc Từ Liêm.
- Phía Nam giáp huyện Hoài Đức.
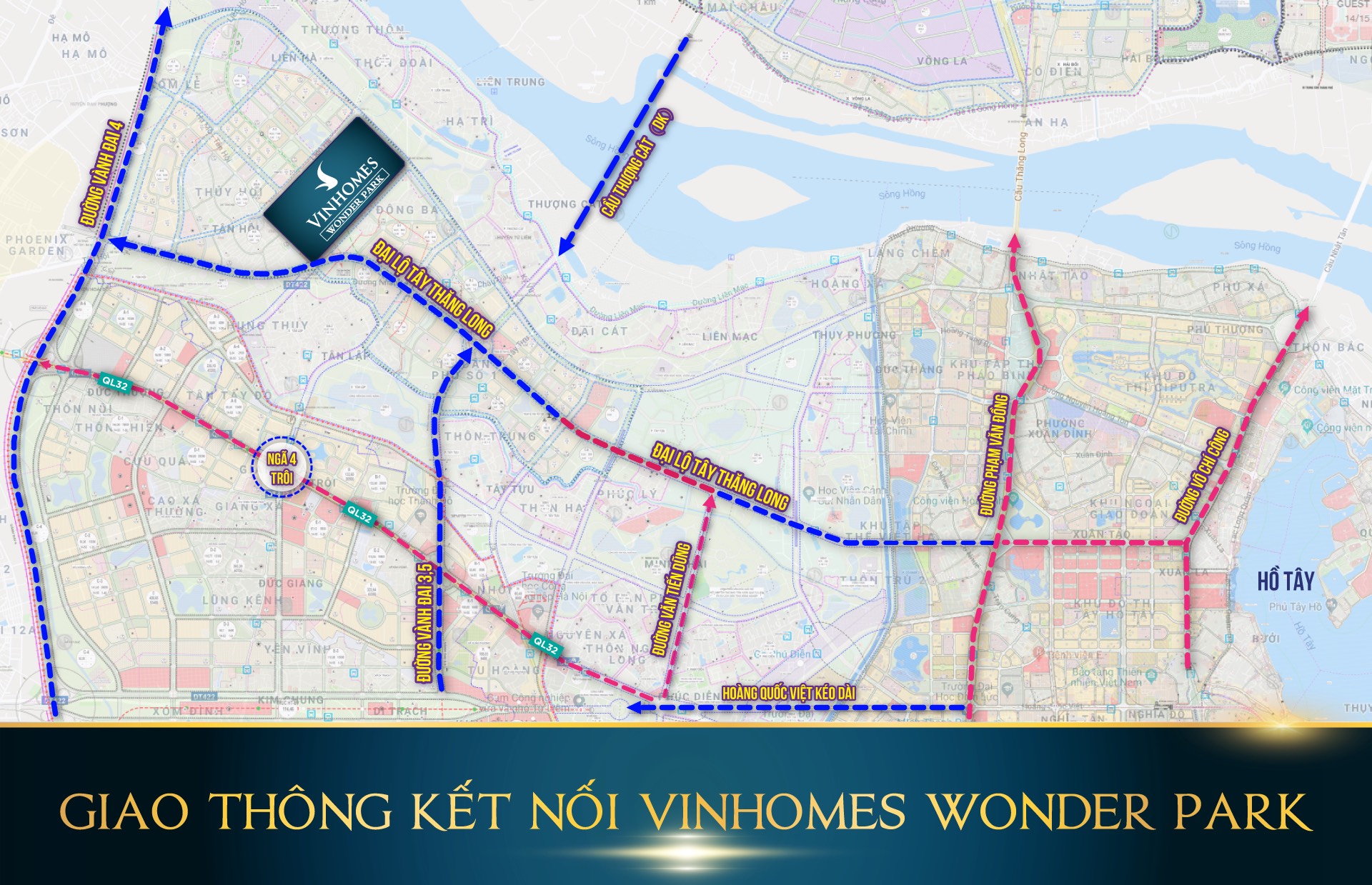
- Đặc biệt : Vinhomes Đan Phượng nằm gần các trục đường huyết mạch từ các huyện phía Tây đi vào trung tâm thủ đô như quốc lộ 32, đường Tây Thăng Long, và trong tương lai sẽ là tuyến đường vành đai 4, đường Hoàng Quốc Việt (kéo dài). Đó sẽ là những sự kết nối tuyệt vời với trung tâm Hà Nội khi mà chỉ mất khoảng 15 phút di chuyển là các cư dân của Vinhomes Đan Phượng đã có mặt ở trung tâm Hà Nội.
- Trong tương lai không xa, Đan Phượng cùng với 3 huyện Gia Lâm, Thanh Trì, Đông Anh sẽ được xây dựng trở thành quận, chính vì vậy Vinhomes Đan Phượng sẽ là điểm đầu tư lý tưởng hàng đầu cho các nhà đầu tư địa ốc. ..
Dự án Vinhomes Đan Phượng được quy hoạch theo đô thị xanh tương lai
Được đặt tên là Vinhomes Wonder Park – Thành phố xanh được quy hoạch và đầu tư hạ tầng theo chuẩn mực quốc tế với các tuyến đường nội bộ rộng từ 13 – 26 mét, vỉa hè phủ kín mảng xanh, hệ thống viễn thông, điện âm, nước thủy cục, hệ thống thoát nước mưa và nước thải riêng biệt…
Hệ thống tiện ích và các dãy nhà phố, biệt thự của Vinhomes Đan Phượng cũng được bố trí hài hòa, hợp lý tạo ra một không gian sống sang trọng, đẳng cấp cho cư dân.
Nhằm hướng tới xây dựng một khu đô thị sinh thái mang tầm cỡ quốc tế, Vinhomes Đan Phượng mang trong mình những điểm nhấn về kiến trúc cũng như cảnh quan thiên nhiên đặc sắc, đảm bảo cho cư dân trong khu đô thị được hòa mình vào cuộc sống xanh, cực kỳ thư giãn.
Đan Phượng đã được UBND thành phố Hà Nội phê duyệt Đề án xây dựng để trở thành một quận trong giai đoạn 2020 – 2025, chính vì vậy nơi đây chắc chắn sẽ là điểm đến đầu tư cực kỳ hấp dẫn trong thời gian tới đây. Các ví dụ chứng minh rõ nét nhất về điều này có thể dẫn chứng từ quận Long Biên khi được chuyển đổi từ huyện sang quận.
Theo quy hoạch thì Vinhomes Đan Phượng sẽ là trung tâm đô thị mới của quận Đan Phượng và là điểm đến thu hút lượng cư dân và du khách hàng đầu ở khu vực phía Tây trung tâm Hà Nội.
Vị trí đắc địa, tụ khí sinh tài của Vinhomes Wonder Park Đan Phượng
Vinhomes Đan Phượng nằm gần các trục đường huyết mạch từ các huyện phía Tây đi vào trung tâm thủ đô như quốc lộ 32, đường Tây Thăng Long, và trong tương lai sẽ là tuyến đường vành đai 4, đường Hoàng Quốc Việt (kéo dài).
Đó sẽ là những sự kết nối tuyệt vời với trung tâm Hà Nội khi mà chỉ mất khoảng 15 phút di chuyển là các cư dân của Vinhomes Đan Phượng đã có mặt ở trung tâm Hà Nội.
Trong tương lai không xa, Đan Phượng cùng với 3 huyện Gia Lâm, Thanh Trì, Đông Anh sẽ được xây dựng trở thành quận, chính vì vậy Vinhomes Đan Phượng sẽ là điểm đầu tư lý tưởng hàng đầu cho các nhà đầu tư địa ốc.
Khu đô thị Vinhomes Đan Phượng – Cuộc Sống Hoa Lệ Phía Trời Tây Hà Nội
Được kỳ vọng trở thành biểu tượng kinh tế - du lịch của cả khu vực phía Tây thủ đô, Vinhomes Đan Phượng đang được kiến tạo tại địa bàn hai xã Tân Hội, Liên Trung. Sau một thời gian dài khảo sát kỹ lưỡng, tập đoàn Vingroup đã quyết định sẽ dựng lên ở nơi đây một đại đô thị “xanh” mang tầm vóc quốc tế, đem đến sự thịnh vượng cho cả khu vực Đan Phượng trong tương lai, nhất là khi nơi đây sẽ trở thành quận trong thời gian tới.
Ngày nay mọi người không chỉ tìm kiếm một nơi để ở mà còn phải có một môi trường sống trong lành với đầy đủ các tiện nghi và tiện ích, nơi có thể thư thái và thư giãn để lấy lại cân bằng trong cuộc sống. Do vậy một khu đô thị sinh thái với tràn ngập không gian xanh và vô vàn những tiện ích như Vinhomes Đan Phượng sẽ được rất nhiều người quan tâm và tìm kiếm.
*** Nhắc đến tập đoàn Vingroup chắc hẳn mọi khách hàng và nhà đầu tư của dự án Vinhomes Đan Phượng đều cực kỳ yên tâm về chất lượng của dự án cũng như tiến độ xây dựng và bàn giao sản phẩm. Những siêu dự án của Vin ra mắt thị trường như Vinhomes Riverside, Vinhomes The Harmony, Times City, Royal City, Vinhomes Centre Park,… đều khẳng định vị thế số 1 của Vingroup tại Việt Nam hiện nay.








